特斯拉汽金大全已更新2023(实时/更新中)|环球简讯
特斯拉汽金大全已更新2023(实时/更新中):00861-37566-43074 二:00861-59440-85159 THE ROLE
We are looking for a highly motivated engineer specializing in security process automation and incident response to defend Tesla’s information, infrastructure, and products.
It"s fun to work in a company where employees believe in what they"re doing! The Detection and Incident Response Team is responsible for detecting and responding to threats against our corporate, manufacturing and production environments.
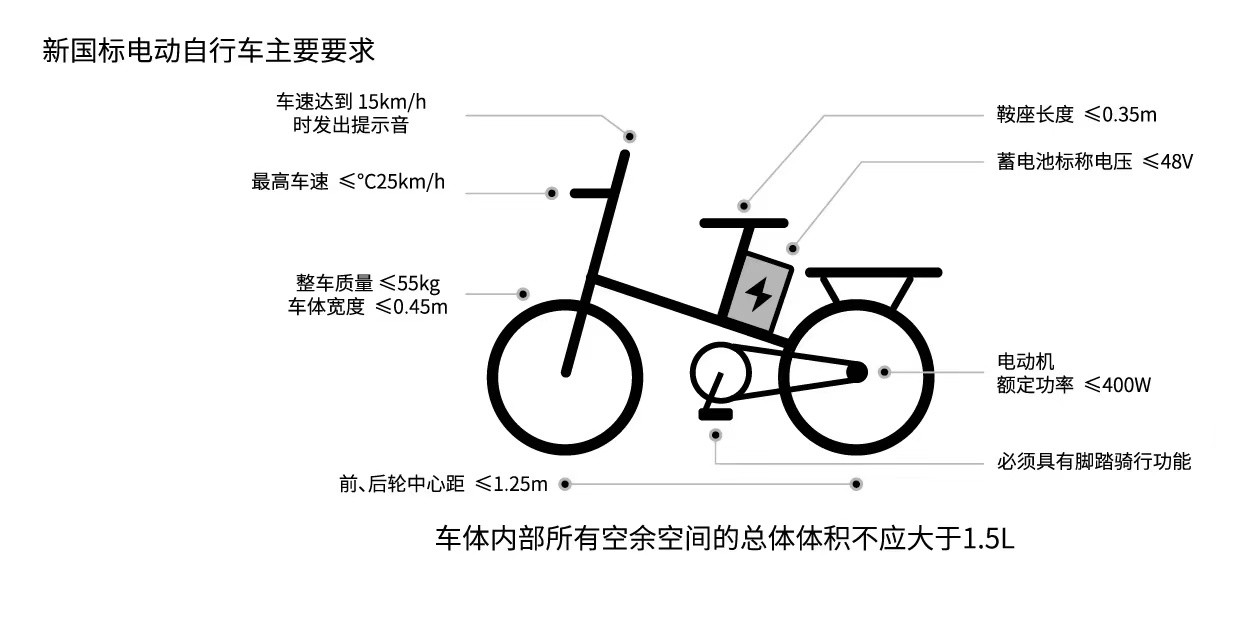
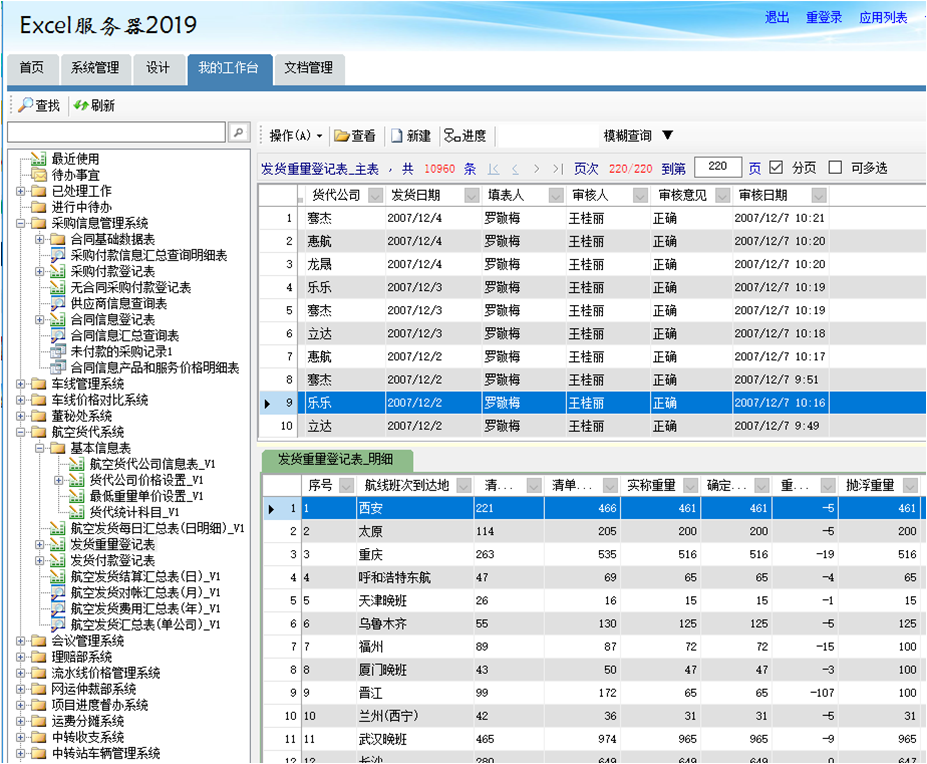
 (资料图片)
(资料图片)
This is a technical role, which is involved in all aspects of the incident response life cycle and what technical steps are needed to automate the process of responding to a security incident. As an Incident Response Engineer, you will be an Incident Handler as part of the Detection and Incident Response team. You will protect Tesla by investigating, containing, remediating, and documenting security incidents. You will also help detection engineers to improve logging coverage, security tools tuning, suggest ideas and contribute to the new signals development process and automation to detect and respond to threats automatically and at scale.
Your responsibilities will also include improving/documenting incident response procedures and playbooks, reporting, and developing and maintaining new automated processes to lower the meantime to remediation.
RESPONSIBILITIES
• Participate in incident management calls and coordinate response, triage, recovery, and reporting of incidents.
• Monthly and quarterly incident analysis and stats reporting.
• Ongoing maintenance and improvements/tuning of automated incident response processes.
• Work closely with the Detection and Threat Intel engineers to detect, respond to alerts and provide timely response for the security incidents .
• Participate in incident response activities (including tabletop exercises) to verify existing playbooks and procedures and identify opportunities for improvement .
• Assessing and analyzing prior incidents for operational improvements, whether automated or manual.
• Continuous monitoring, tuning, hardening and improvement of the existing security rules and policies .
• Keeping existing runbooks up to date and creating new runbooks to improve processes/coverage .
• Analyze security data and report on threats and incidents across various platforms and environments.
• Monitor and analyze emerging threats, vulnerabilities, and exploits.
• Provide security monitoring and incident response services supporting the mission to protect Tesla.
• Security process improvement .
REQUIREMENTS
• Excellent understanding and experience in multiple security domains such as intrusion detection, incident response, malware analysis, application security, and forensics.
• Experience detecting abuse and large-scale attacks in a diverse environment. .
• Experience in cloud environments (AWS preferred) and Linux containers and orchestration systems (Kubernetes preferred) .
• Knowledge of web-services such as API and REST .
• Experience with GIT or other version control systems .
• Basic understanding of the Security automation (SOAR) principles. As a bonus – ability to implement automated solutions outside of the scope of SOAR.
• Experience working with multiple stakeholders such as engineering/operations teams, internal business units, external incident response teams, and law enforcement throughout the incident lifecycle.
• Solid experience and the ability to analyze network traffic, endpoint indicators, IOCs. Ability to combine/search/correlate various log sources to identify potential threats, assess the potential damage, and recommend countermeasures.
• Familiarity with the following detection-related disciplines with deep experience in one or more:
o Large scale analysis of log data using tools such as Splunk or ELK.
o File system, memory, or live response on Windows, MacOS and/or Linux.
o Analysis of network traffic from intrusion detection systems and flow monitoring systems.
o Host level detection with tools such as auditd, os-query, SysMon
• Real world experience using at least one major SIEM system .
• Experience with Splunk is a bonus .
• Security Certifications (i.e. Security+, CISSP, CEH, SANS, etc.) is also a plus .
关键词:
相关阅读
-
特斯拉汽金大全已更新2023(实时/更新中)...
Thisisatechnicalrole,whichisinvolvedinallaspectsoftheincidentre... -
天狗望月的意思怎么解释_天狗望月的意思
1、应该是仙女弹琴,不是羡慕弹琴。2、出自《黄山奇石》课文在义务... -
观焦点:末日狂欢全文免费阅读_末日狂欢
1、非常幸运,深入研究以后我不用进行这样的工作了,“末日狂欢”是... -
阿尔法S先行版亮相华中国际车展!10万差...
在知名汽车媒体Autolab组织的《2021冬季续航测试》中,极狐阿尔法S... -
奔腾小马,年轻人这点爱好你算是玩明白了
车尾部分则采用了与前灯组相呼应的设计风格,让整车线条非常协调。... -
全球速看:仅用15个月 AITO问界第10万...
北京商报讯(记者刘晓梦)5月27日,仅用15个月,AITO问界第10万辆量...
- 特斯拉汽金大全已更新2023(实时/更新中)|环2023-05-27
- 全球视讯!厦门港多个码头榜上有名 2022年2023-05-27
- 建设“数字+行业”专业园区 推动厦门软件2023-05-27
- 厦门首条直飞巴黎航线来了2023-05-27
- 环球播报:本周末厦门天气晴好 后天起受台2023-05-27
- 环球时讯:今天,厦门市数字体育产业园正式2023-05-27
- 司机拒给救护车让路:“扣分怎么办,我凭啥2023-05-27
- 当前速看:夏季游泳有了新去处!华科大游泳2023-05-27
- 71岁加拿大男子花54年拿到学士学位,或成世2023-05-27
- 嫌疑人在加油,美国警察用电击枪缉捕致其烧2023-05-27
- 男子半夜盗窃,得手后对着监控嚣张“电摇嘲2023-05-27
- 实时焦点:极目锐评|男演员减肥食谱吸引网2023-05-27
- 女子养了4年的爱犬被人活生生压死,面对视2023-05-27
- 世界即时:定了!6月2日,武汉种博会开幕2023-05-27
- 通山举办校园“小戏迷”戏曲比赛2023-05-27
- 天天报道:为科创企业提供贴身司法服务 武2023-05-27
- 杭州这场健步行活动太有意思!游泳世界冠军2023-05-27
- 当前播报:北京电视台主持人高飞_丰台电视台2023-05-27
- 天狗望月的意思怎么解释_天狗望月的意思2023-05-27
- 观焦点:末日狂欢全文免费阅读_末日狂欢2023-05-27
- 关晓彤男朋友的接吻_关晓彤的男朋友是谁_全2023-05-27
- 阿尔法S先行版亮相华中国际车展!10万差价2023-05-27
- 奔腾小马,年轻人这点爱好你算是玩明白了2023-05-27
- 全球速看:仅用15个月 AITO问界第10万辆量2023-05-27
- 天天快消息!全新林肯冒险家vs宝马X1,真越2023-05-27
- 厦门港多个码头榜上有名 2022年度中国港口2023-05-27
- 建设“数字+行业”专业园区 推动厦门软件2023-05-27
- 【天天快播报】本周末厦门天气晴好 后天起2023-05-27
- 厦门首条直飞巴黎航线来了 观察2023-05-27
- 今天,厦门市数字体育产业园正式揭牌!2023-05-27